Ransomware Policy Template - What is a ransomware incident response (ir) playbook? These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. This playbook template is intended to outline a structured and specific approach in. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the business.
What is a ransomware incident response (ir) playbook? Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. This playbook template is intended to outline a structured and specific approach in. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Ransomware offers a unique and pressing threat to the business.
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. This playbook template is intended to outline a structured and specific approach in. Ransomware offers a unique and pressing threat to the business. What is a ransomware incident response (ir) playbook? Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills.
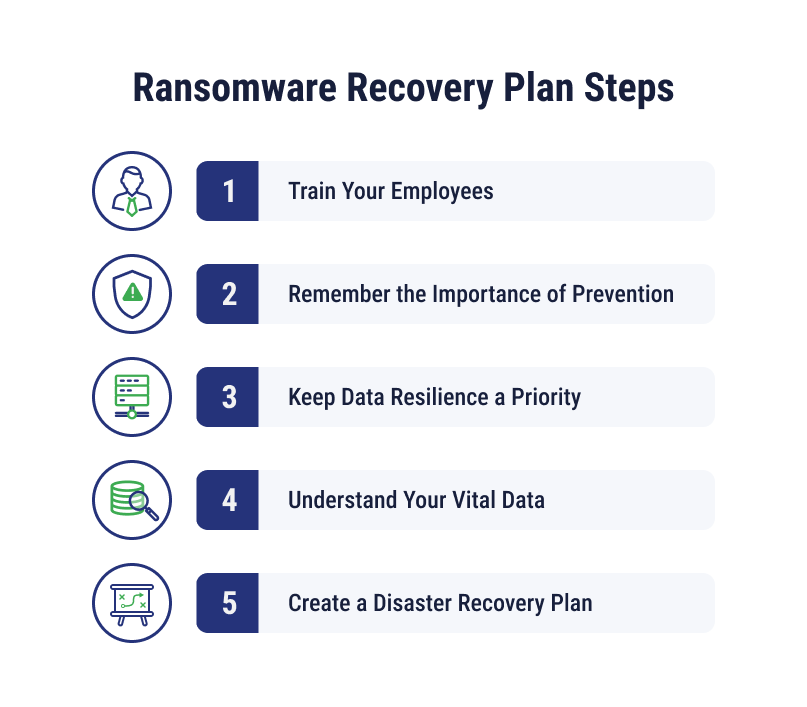
5Step Ransomware Incident Response Plan CloudAlly
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. This playbook template is intended to outline a structured and specific approach in. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the business. What is a ransomware incident response (ir).
Ransomware Policy Template
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. What is a ransomware incident response (ir) playbook? Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the business. This playbook template is intended to outline a structured and specific approach.
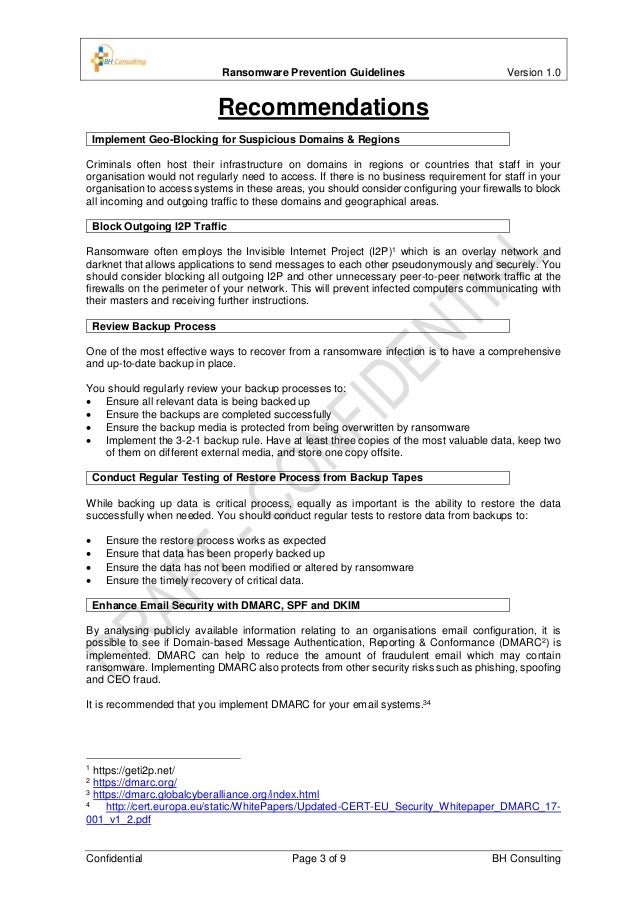
Ransomware Incident Response Plan Template 1 Introduction, Policy and
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. This playbook template is intended to outline a structured and specific approach in. What is a ransomware incident response (ir) playbook? Ransomware offers a unique and pressing threat to the business. Build a ransomware‑ready backup policy with access controls, offline backups, and restore.
Ransomware Response Playbook Policy Template Banking and Fintech
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Ransomware offers a unique and pressing threat to the business. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. This playbook template is intended to outline a structured and specific approach in. What is a ransomware incident response (ir).
How to Develop a Ransomware Recovery Plan & Prevent an Attack
This playbook template is intended to outline a structured and specific approach in. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. What is a ransomware incident response (ir) playbook? Ransomware offers a unique and pressing threat to the.
Ransomware Response Playbook Policy Template Banking and Fintech
This playbook template is intended to outline a structured and specific approach in. What is a ransomware incident response (ir) playbook? These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the.
Ransomware Policy Template
Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. This playbook template is intended to outline a structured and specific approach in. What is a ransomware incident response (ir) playbook? Ransomware offers a unique and pressing threat to the business. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure.
Ransomware Policy Template
Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. What is a ransomware incident response (ir) playbook? Ransomware offers a unique and pressing threat to the business. This playbook template is intended to outline a structured and specific approach in. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure.
Ransomware Policy Template
Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the business. This playbook template is intended to outline a structured and specific approach in. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. What is a ransomware incident response (ir).
Ransomware Policy Template
These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Ransomware offers a unique and pressing threat to the business. What is a ransomware incident response (ir) playbook? Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. This playbook template is intended to outline a structured and specific approach.
What Is A Ransomware Incident Response (Ir) Playbook?
This playbook template is intended to outline a structured and specific approach in. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security. Build a ransomware‑ready backup policy with access controls, offline backups, and restore drills. Ransomware offers a unique and pressing threat to the business.