Five Forms Of Conflict - These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Also see our blog post by health care ethics advisor jane. Box plots are used as a visual. Five wishes offers suggestions for choosing the right person and naming alternate choices. Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical.
Box plots are used as a visual. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Also see our blog post by health care ethics advisor jane. Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Five wishes offers suggestions for choosing the right person and naming alternate choices.
Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. Also see our blog post by health care ethics advisor jane. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Box plots are used as a visual. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Five wishes offers suggestions for choosing the right person and naming alternate choices.
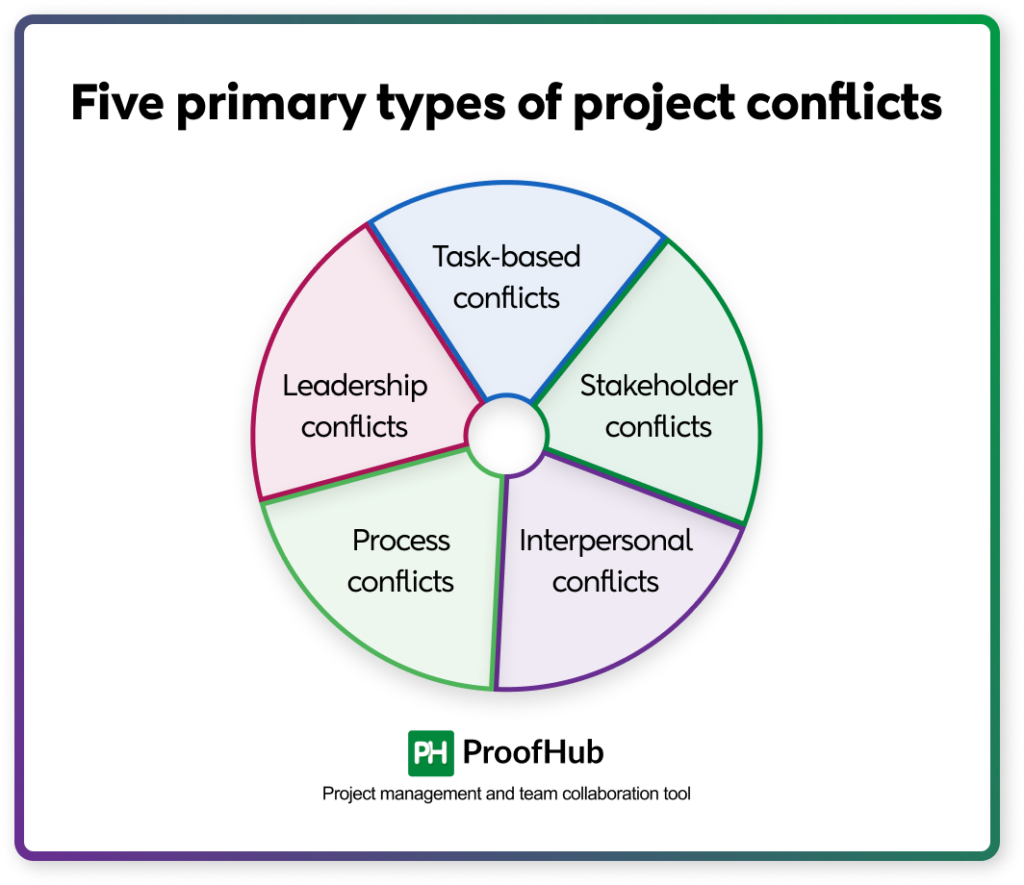
Conflict Management in Projects Causes, Prevention & Solutions
It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Five wishes offers suggestions for choosing the right person and naming alternate choices. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Love languages everyone has a.
5 Various Styles of Conflict Resolution Infographics Conflict
These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. Also see our blog post by health care ethics advisor jane. It is used to determine the variability.
5 Types of Conflict Types of conflict, Writing tips, How to memorize
Five wishes offers suggestions for choosing the right person and naming alternate choices. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Box plots are used as a visual. It is used to determine the variability (or the differences in data) of a data set and to construct.
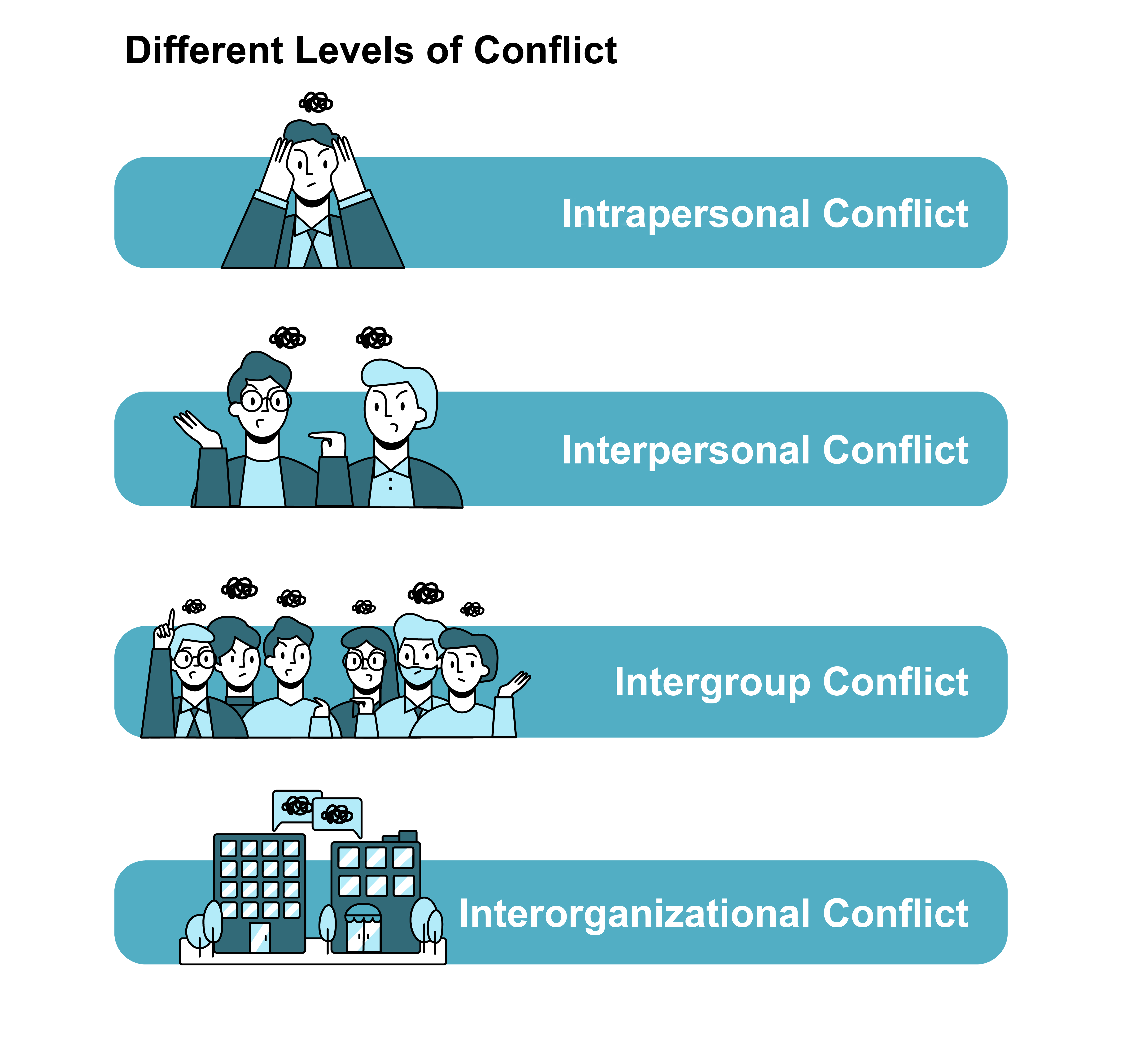
1.2 Levels and Types of Conflict Conflict Management
Also see our blog post by health care ethics advisor jane. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Box plots are used as a visual. It is used to determine the variability (or the differences in data) of a data set and to construct box plots..
Top Conflict Management Strategies along with 5 styles
Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. Five wishes offers suggestions for choosing the right person and naming alternate choices. Box plots are used as a visual. These five functions were included in the core because they represent the five primary pillars for a successful and.
The Five 5 Types of Conflict In A Relationship.
Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. Box plots are used as a visual. It is used to determine the variability (or the differences in.
PPT A road map to identifying five types of conflict PowerPoint
Also see our blog post by health care ethics advisor jane. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Box plots are used as a visual. Five wishes offers suggestions for choosing the right person and naming alternate choices. Love languages everyone has a love tank we.
Introduction to conflict styles
These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Also see our blog post by health care ethics advisor jane. Five wishes offers suggestions for choosing the.
Conflict Management Strategies in the Workplace Examples
Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. Five wishes offers suggestions for choosing the right person and naming alternate choices. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity. It is used to determine.
How Many Conflict Management Styles Are There?
Love languages everyone has a love tank we receive love differently there are five primary love languages words of affirmation physical. It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Also see our blog post by health care ethics advisor jane. These five functions were included in the.
Five Wishes Offers Suggestions For Choosing The Right Person And Naming Alternate Choices.
It is used to determine the variability (or the differences in data) of a data set and to construct box plots. Box plots are used as a visual. Also see our blog post by health care ethics advisor jane. These five functions were included in the core because they represent the five primary pillars for a successful and holistic cybersecurity.